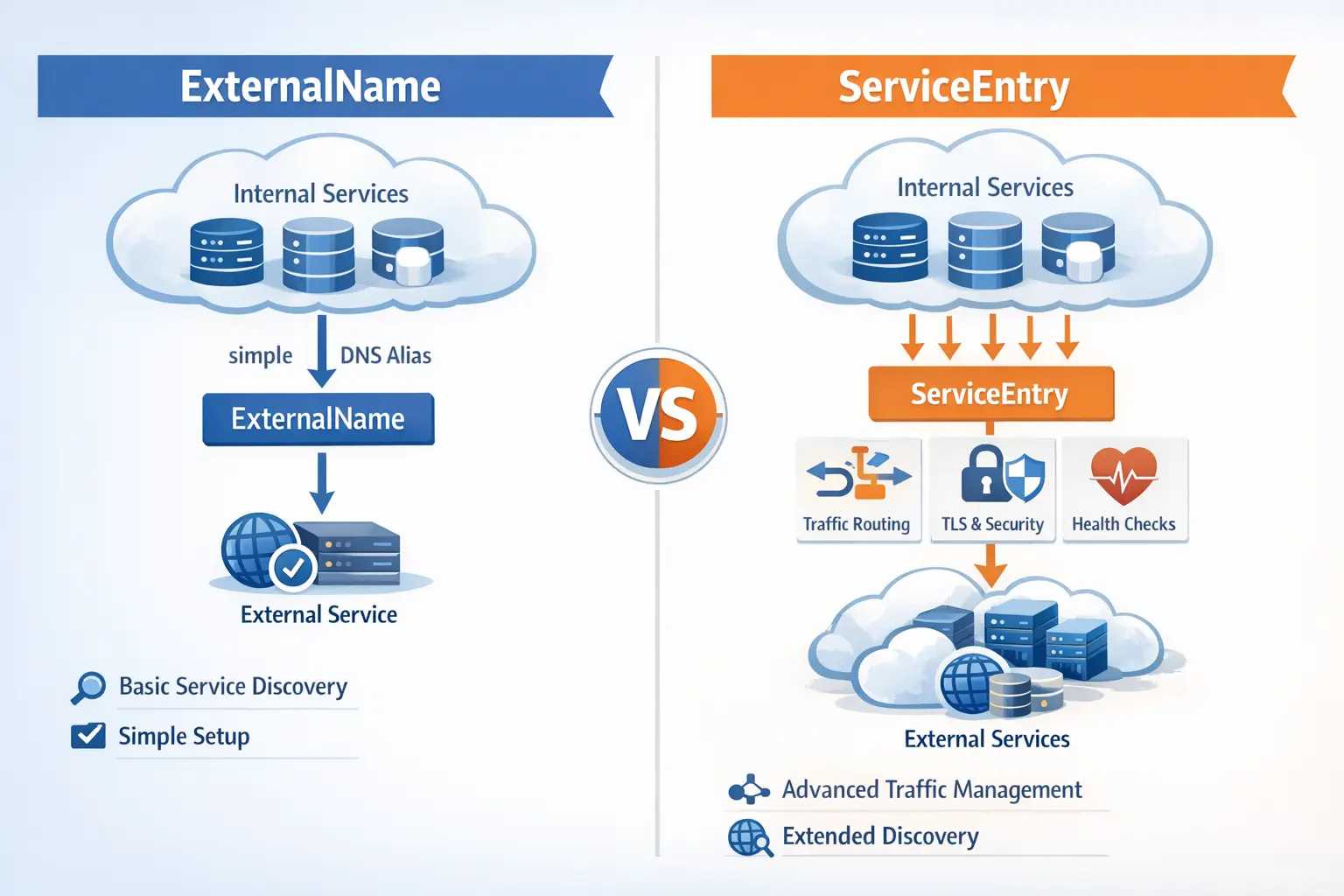
As Kubernetes continues to evolve, Istio features are gradually finding corresponding implementations in Kubernetes, such as Sidecar containers, Gateway API, and the topic of this article: ExternalName. Both ExternalName and ServiceEntry can serve to introduce external services to Kubernetes clusters, but their functionality and use cases differ. This article will provide a detailed analysis.
ExternalName vs ServiceEntry
The table below compares ExternalName and ServiceEntry from multiple aspects:
| Feature/Use Case | ExternalName | ServiceEntry |
|---|---|---|
| Traffic Control | Limited, only supports TCP and UDP | More flexible, supports TCP, UDP, HTTP, and other protocols, can specify ports, TLS, and other options |
| Service Discovery | Suitable for simple aliases to external services | Suitable for describing services inside and outside the mesh, including detailed configuration of external and internal services |
| Configuration Complexity | Simple, suitable for basic service discovery needs | More complex, suitable for scenarios requiring advanced traffic control and detailed configuration |
| TLS Support | Limited, relatively simple | Richer TLS support, can specify certificates and other detailed options |
| Security | Basic, suitable for simple use cases | More powerful security support, can define options like subjectAltNames |
| Purpose | Suitable for simple external service aliases | Suitable for complex traffic management and service discovery needs, especially in multi-protocol and complex network topologies |
Use Cases
When to use ExternalName:
- Simple Service Aliases: When external services only need a simple alias without complex traffic control,
ExternalNamecan be used. - No Detailed Traffic Control Requirements: When you don’t need detailed control over service traffic and only need simple service alias access, choose
ExternalName.
When to use ServiceEntry:
- Complex Traffic Control Requirements: When you need more complex traffic control, such as specifying protocols, ports, TLS options, etc., choose
ServiceEntry. - Describing Services Inside and Outside the Mesh: When you need to describe services both inside and outside the mesh, including detailed configuration of external and internal services,
ServiceEntryis more suitable. - Requirements for Detailed Service Attributes: When you need to define special attributes for services, such as
subjectAltNames, you must useServiceEntry.
Potential Issues When Using ExternalName in Istio
Before Istio 1.20, when an ExternalName-type Service existed in the mesh, if the Service’s port overlapped with other external services’ ports, traffic might be incorrectly routed to that ExternalName Service. This issue was resolved in Istio 1.20. See Better support ExternalName #37331 for details.
Summary
In service mesh selection, ExternalName and ServiceEntry respectively provide simple service aliases and more complex traffic management and service discovery options. ExternalName is suitable for simple external service aliases, while ServiceEntry has advantages in handling complex traffic control and services both inside and outside the mesh. In practical applications, flexibly choose the appropriate mechanism based on specific needs and configuration complexity. As Istio and Kubernetes continue to evolve, the usage of these features may be affected, so keeping up with relevant community updates and best practices is key to maintaining system health and efficient operation. Choosing the right service mesh components will help build reliable, secure, and highly scalable microservice architectures.