In a microservice architecture, API gateways often need to perform high-level request and response processing tasks such as authentication, data transformation, and security checks. Envoy’s ext_proc external processing filter is a powerful tool that enables flexible request and response handling by interacting with a gRPC service. This article delves into its features, configuration, and performance optimization strategies to help developers and DevOps engineers effectively utilize this capability.
Relationship Between ext_proc and Other Filters
The ext_proc filter shares similarities with other gRPC-based filters in Envoy, such as ext_authz. However, ext_proc offers more extensive capabilities, supporting full request and response processing. This makes it particularly suitable for scenarios requiring deep content inspection and modification.
Refer to the following mind map for a quick overview of Envoy’s ext_proc external processing filter:

This mind map illustrates the core structure and functional modules of Envoy’s ext_proc filter. Using a bidirectional gRPC stream protocol, ext_proc communicates with external services, enabling flexible HTTP request and response handling, including synchronous and asynchronous processing.
How ext_proc Works and Its Configuration
Definition and Functionality
ext_proc is an Envoy HTTP filter that delegates request and response processing to a gRPC service, allowing complex logic implementation in external services to meet specific business requirements.
Working Mechanism
ext_proc uses a bidirectional gRPC stream to communicate with an external service, enabling real-time request and response processing interaction. Envoy can offload complex tasks such as authentication, data transformation, and custom header manipulation to an external service, improving flexibility and scalability.
Envoy sends ProcessingRequest messages, and the external service returns ProcessingResponse messages. Importantly, this gRPC stream is created per HTTP request stream; it is not shared among multiple requests. Each HTTP request handled by Envoy creates its own dedicated gRPC stream, ensuring isolation and precise request-response management. This design allows the external service to intervene at various stages of the request and response lifecycle, even generating entirely new responses.
Here’s a sequence diagram illustrating the process:

Key Features
- Request and Response Handling: Read and modify HTTP request and response headers, bodies, and trailers.
- Flexibility: Define custom logic based on business needs, extending built-in functionality.
- Asynchronous Processing: Support for asynchronous processing to prevent request blocking.
Envoy Configuration Example
Below is a basic Envoy configuration example:
| |
To understand the connection between Envoy configuration and a gRPC service, consider how the following configuration items influence traffic processing:
- grpc_service: Defines the target address and cluster name for communication with the gRPC service, corresponding to
ext_proc_clusterin Envoy’s configuration. - processing_mode: Controls when to trigger processing stages such as request headers, request bodies, and response headers, determining when to invoke the gRPC service.
- failure_mode_allow: Specifies whether to continue request processing when the gRPC service fails, ensuring high availability in partial failure scenarios.
- listeners: Defines the network address and port where Envoy listens for incoming requests.
- filter_chains: Configures the request processing chain, including the HTTP connection manager and external processing filters.
- http_filters: Lists the enabled filters, such as
ext_procandrouter. - clusters: Defines upstream services and the location of the external processing gRPC service.
You can see the configuration instructions in the Envoy documentation.
Envoy uses these configuration options to offload request and response processing to the gRPC service. The results are returned through a bidirectional streaming protocol, influencing request-forwarding behavior.
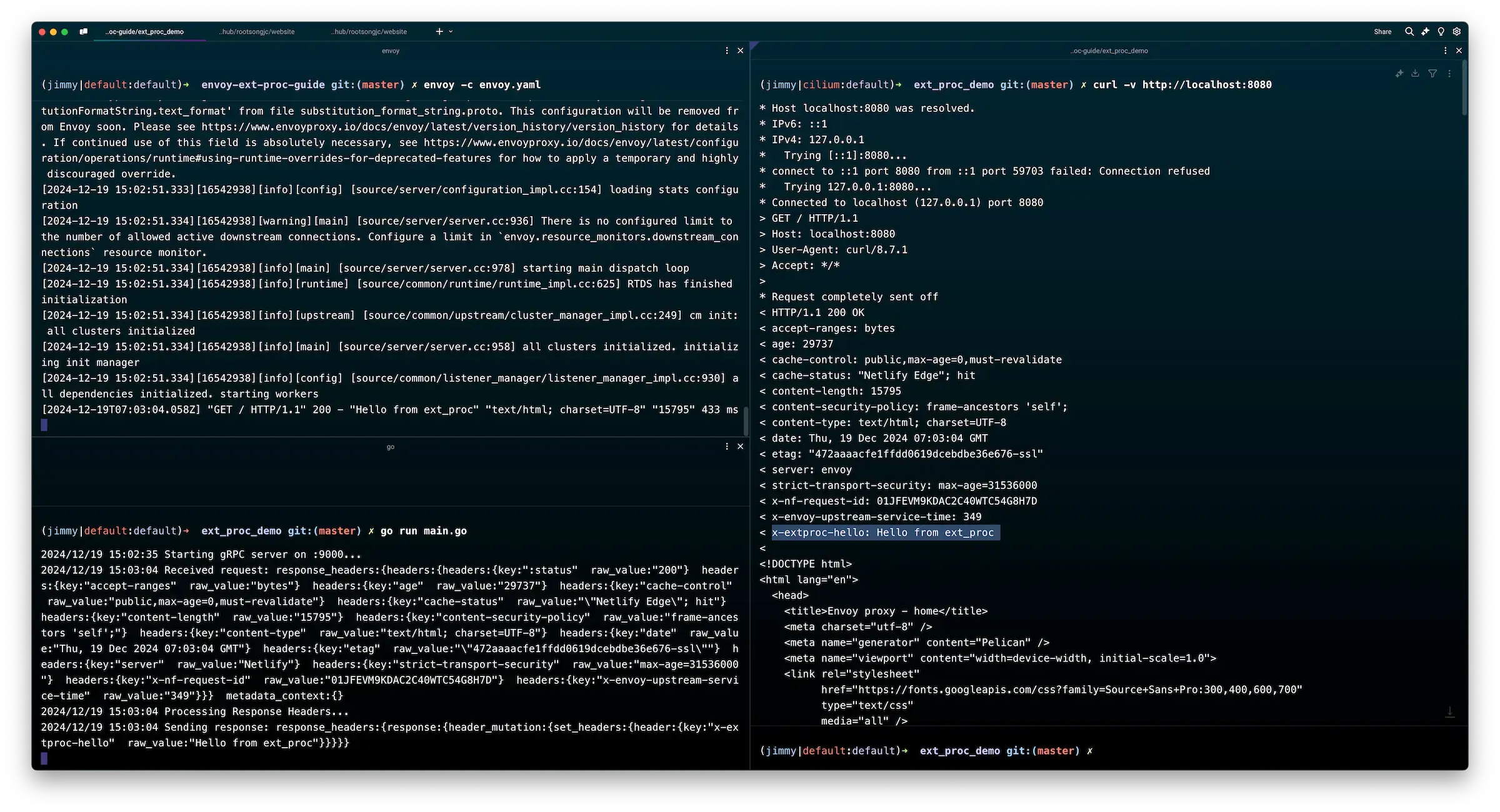
gRPC Service Example
Below is a simple gRPC external processing server implementation demonstrating how to add custom response headers using ext_proc. This example highlights key method choices and design decisions, such as using the Process method to continuously receive requests and send responses, ensuring seamless processing. It also leverages the HeaderMutation configuration to modify HTTP response headers, illustrating the tight integration between gRPC messages and Envoy’s configuration for dynamic extension and flexible management.
| |
Expected Result: The request returns a status code of 200, with a custom header x-extproc-hello: Hello from ext_proc in the response. If the header is missing, check the following:
- Is the gRPC service running? Ensure the gRPC server has started and is listening on port
:9000. - Is the Envoy configuration correct? Verify the Envoy configuration file to ensure the
ext_procfilter is enabled and that theext_proc_clusterconfiguration is correct. - Logs and Error Investigation: Check the logs of both Envoy and the gRPC server for potential errors.
Running Envoy and the gRPC service locally, you can test with:
envoy -c envoy.yaml
go run main.go
curl -v http://localhost:8080
You’ll see a response including the custom header x-extproc-hello: Hello from ext_proc.
Metrics and Monitoring
ext_proc generates statistics under the http.<stat_prefix>.ext_proc. namespace, where stat_prefix is the HTTP connection manager prefix. Common metrics include:
| Metric Name | Type | Description |
|---|---|---|
| streams_started | Counter | Number of started gRPC streams |
| streams_msgs_sent | Counter | Number of messages sent |
| streams_msgs_received | Counter | Number of messages received |
| spurious_msgs_received | Counter | Number of unexpected messages received |
| streams_closed | Counter | Number of successfully closed streams |
| streams_failed | Counter | Number of streams with gRPC errors |
| failure_mode_allowed | Counter | Number of ignored failures (per config) |
| message_timeouts | Counter | Messages timed out without response |
| rejected_header_mutations | Counter | Rejected header modifications |
| clear_route_cache_ignored | Counter | Ignored clear route cache requests |
| clear_route_cache_disabled | Counter | Disabled clear route cache requests |
For more details, refer to the Envoy documentation.
Use Cases and Optimization Strategies
Common Use Cases
- Authentication: External authentication services check user credentials.
- Data Auditing: Log request and response data for compliance purposes.
- Traffic Management: Adjust traffic routing based on dynamic analysis.
Configuration Tips and Optimization Strategies
- Failure Recovery and Load Balancing: Deploy multiple instances of the gRPC service with load balancing.
- Message Timeouts and Retries:
http_filters:
- name: envoy.filters.http.ext_proc
config:
grpc_service:
envoy_grpc:
cluster_name: ext_proc_server
processing_mode:
request_header_mode: SEND
response_header_mode: SEND
message_timeout: 500ms
max_message_timeout: 1000ms
failure_mode_allow: false
- Metadata Options and Security Policies:
metadata_options:
forwarding_namespaces:
untyped: ["custom_namespace"]
Conclusion
Envoy’s ext_proc filter provides robust support for service governance, data transformation, and request inspection through flexible request and response processing capabilities. Correctly configuring and optimizing ext_proc can significantly enhance system flexibility and scalability to meet diverse business requirements.